A ransomware attack can shut down a business for weeks, damage reputation with customers and employees, and open the door for further data breaches. As an attack can be devastating, knowing how to prevent ransomware is an essential skill of any cybersecurity team.
This article explains how to prevent ransomware from infecting your business. Read on to learn how to counter the ransomware threat and build a company-wide culture of awareness that stops these dangerous breach attempts.

What is Ransomware? How Does it Work?
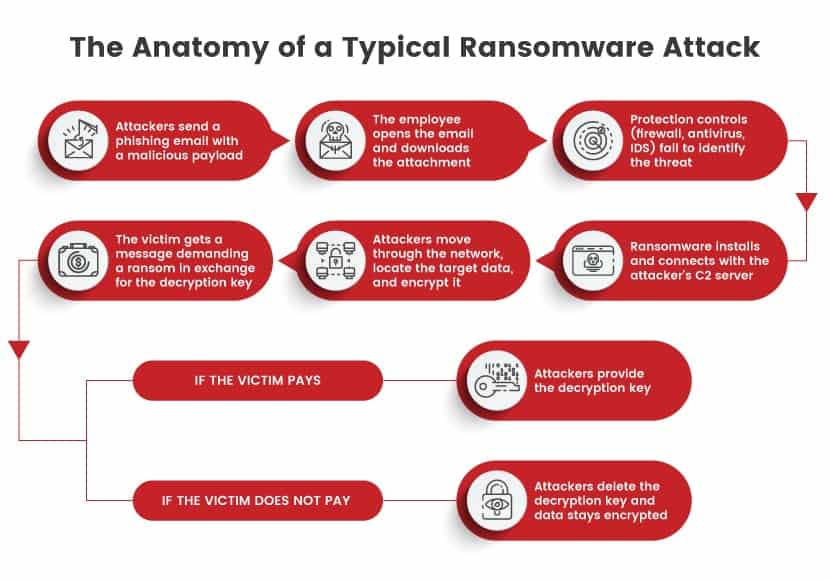
Ransomware is a type of malware that encrypts or locks the victim’s data. Attackers then demand a ransom in exchange for a unique key to decrypt or unlock the files. Like all malware, a ransomware attack starts when a malicious payload enters the system, which typically happens via:
- A corrupt link or attachment.
- An ad that leads to a website with an exploit kit.
- A worm that exploits a system weakness.
- A drive-by download.
- An infected piece of hardware.
The most common method of starting a ransomware attack is with a phishing email. The email typically relies on social engineering to encourage the recipient to click a link or download an attachment. If the user falls for the trick, the malware silently installs on the device.
Once the malware is inside the network, the program spreads to connected systems and searches for valuable data. If the program encrypts the data, the victim receives a note that demands payment in cryptocurrency in exchange for the decryption key. Otherwise, attackers threaten to destroy the key or leak sensitive information.
Our article about the most common ransomware examples demonstrates both the variety and effectiveness of these cyberattacks.
How to Prevent Ransomware Attacks: Best Practices
Ransomware is a danger to both SMBs and enterprises, so companies of all sizes should know how to prevent this cyber threat. Below are the most effective methods of ensuring your business does not fall victim to ransomware.
Set Up a Firewall
A firewall is the first software-based line of defense against ransomware. Firewalls scan the incoming and outgoing traffic for potential risks, allowing the security team to monitor for signs of malicious payloads.
To support your firewall activity, consider setting up:
- Active tagging of workloads.
- Threat hunting.
- Consistent evaluation of traffic for mission-critical applications, data, or services.
Ideally, your firewall should have the ability to run deep packet inspection (DPI) to examine the data content. This capability automatically identifies packages with infected software.
Read about the different types of firewalls you can set up to protect your business from ransomware and other cyber threats.
Use Immutable Backups
An immutable backup operates like any data backup, but it does not allow anyone to change or delete information. This type of backup is the ideal protection against data corruption, whether malicious or accidental. If you fall victim to a ransomware attack, an immutable backup ensures that:
- You do not have to pay the ransom to get your data back.
- Your business does not suffer a prolonged outage.
- Hackers cannot encrypt data even if they reach the backup storage.
You should back up your data multiple times a day, use at least two backups, and keep one instance offline. If you suffer a ransomware infection, wipe your old system, and recover the last clean backup you have on record.
Remember that losing private customer information to criminals is still an issue even if you can restore the data. Hackers can sell or leak the info, so take time to set up other precautions besides an immutable backup.
Segment Your Network
Once ransomware enters your system, the malware needs to move laterally through the network to reach target data. Network segmentation prevents intruders from moving freely between systems and devices. Ensure each subsystem in the network has:
- Individual security controls.
- Strict and unique access policies.
- A separate firewall and gateway.
If intruders compromise a part of your network, segmentation prevents them from reaching target data. Attackers need time to break into each segment, which gives the security team more time to identify and isolate the threat.
Our introduction to network security explains how companies set up their networks and keep intruders away from sensitive data.
Build Staff Awareness
Employees are the most vulnerable attack surface for a ransomware attack. Organize regular security awareness training that explains the role staff plays in preventing ransomware and ensure employees know how to:
- Recognize the signs of a phishing attack.
- Safely download and install applications.
- Recognize suspicious executable files and links.
- Keep their credentials safe.
- Choose strong passwords.
- Keep their systems up to date.
- Verify software and website legitimacy.
Besides covering cybersecurity best practices, staff training should also stress the importance of reporting suspicious activity if something looks off.
Read about spear phishing, a common infection technique hackers use when launching a highly targeted ransomware attack.
Run Regular Security Tests
Vulnerability assessments enable you to check a systems for weaknesses. These tests inspect the IT environments for potential exploits, such as:
- System misconfigurations.
- Issues in staff behavior.
- Weaknesses that allow the setup of backdoor programs.
- Flaws in account privileges.
- Problems with authentication mechanisms.
- Unpatched firewalls, apps, and OSs.
- Weak passwords.
- Database errors that allow SQL injections.
For a more realistic analysis, consider organizing a full-blown pen test. Penetration testing mimics real-life attempts to breach a system, so run occasional ransomware simulations to see how well your system and staff respond to the threat.
Whitelist Applications
Blacklisting and whitelisting are two standard methods for controlling what software employees can install on their devices:
- Blacklisting is the practice of blocking the installation of specific pieces of software.
- Whitelisting permits the installation of particular programs and blocks the installation of all other software.
While blacklisting is effective in specific scenarios, whitelisting is a more efficient method of preventing ransomware. Whitelist apps employees can install on their computers to prevent someone from accidentally installing an infected program. You can also whitelist websites for further security control.
Set up a Sandbox
Sandboxes are isolated environments that can run programs and execute files without affecting the host device or network. While typically a part of software testing, a sandbox can also help cybersecurity teams test potentially malicious software.
Using a sandbox for malware detection adds another layer of protection against different cyberattack types, including ransomware.
Enforce Strong Password Security
Your staff must know the importance of strong passwords. Unfortunately, average password practices leave a lot of room for improvement:
- On average, 3 out of 4 people use the same password for multiple purposes.
- Around a third of Internet users rely on a significantly weak password, like abc123 or 123456.
Remember that ransomware attacks often start by exploiting loose employee behavior. Ensure all employees have strong passwords they update regularly. Otherwise, attackers can breach your system with a simple brute-force attack.
Also, consider using multifactor authentication that requires users and employees to verify identities in multiple ways before accessing a system.
For additional security and control over your staff’s credentials, consider deploying a password management solution.
Improve Endpoint Protection
Endpoint security emphasizes the protection of the network’s endpoints, including:
- Laptops.
- Tablets.
- Mobile phones.
- Internet-of-things devices.
All wireless devices that use your network are a potential entry point for ransomware. Protect these devices from hackers by:
- Blocking traffic and apps that are prone to cyber threats.
- Warning employees when they visit a risky website.
- Checking if devices have the latest patches.
Good endpoint protection also grants admins real-time visibility when an intruder compromises a device, allowing them to react to potential breaches quickly.

Timely Software Patches
Ransomware often exploits security loopholes and bugs within the company’s software, whether for initial infection or lateral movement. Keep software up to date with the latest updates and patches to ensure optimal protection of:
- Apps.
- Anti-malware programs.
- Endpoint protection.
- Intrusion detection and prevention system (IDPS).
- Firmware.
- Operating systems.
- Firewalls.
- Third-party software.
Remember that ransomware evolves like any other malware. Attackers adapt their strategies to the latest vulnerabilities, so even waiting a few days to update a system is a considerable risk.
Improve Your Email Security
Email security best practices are crucial to countering phishing and other social engineering traps. Your mail server should:
- Filter out incoming emails with files that have suspicious extensions, such as .vbs and .scr.
- Automatically reject addresses of known spammers and malware.
Technologies you can use to protect your company emails are:
- Sender Policy Frameworks (SPFs).
- Domain Message Authentication Reporting and Conformance (DMARC).
- DomainKeys Identified Mail (DKIM).
Consider also deploying a third-party email scanning tool for additional protection. This tool helps discover and isolate ransomware attempts before the file reaches the employee.
Employ the Principle of Least Privilege
All your users and employees should only have the level of access they require to perform their roles. A graphic designer in the Marketing team, for example, should not have access to the account details available to the Sales team.
Restricted access limits the damage of a potential ransomware attack. If an intruder compromises one of your employees, the stolen credentials will not allow the attacker to move between systems.
Learn more about zero-trust security, an essential aspect of protecting a complex IT environment.
Set Up Ad Blockers
Ensure all employee devices and browsers have plug-ins and extensions that automatically block pop-up ads. Malicious marketing is a common ransomware source, and blocking ads is a simple way to limit the attack surface.
Block Script Executions
A common tactic ransomware hackers use is to send .zip files with malicious JavaScript code. Another popular strategy is to pack a .vbs (VBScript) file into a .zip archive.
Prevent this vulnerability by disabling Windows Script Host and remove the devices’ ability to execute scripts.
Display File Extensions
Ransomware hackers often disguise the malicious payload within a file name such as Paychecks.xlsx, hoping to trick the user into clicking the attachment. If employees set their device to display file extensions, they would see that the file’s real name was Paychecks.xlsx.exe.
Ensuring all employees can see file extensions reduces the chance of accidentally opening a corrupt payload that starts an attack.
Use a CASB
If your team uses cloud services, a cloud access security broker (CASB) is an excellent counter to ransomware. A CASB is either an on-prem or cloud-based software that acts as an intermediary between cloud users and data. This tool is essential to cloud security and has multiple purposes, including:
- Securing data flows between in-house setups and cloud environments.
- Monitoring all cloud activity.
- Enforcing security policies.
- Ensuring compliance.
Learn why companies create cloud security policies, official guidelines that instruct employees how to use cloud services correctly.
Bring-Your-Own-Device (BYOD) Restrictions
Unregulated use of employee’s devices poses an unnecessary risk to a network. You can write a BYOD policy that outlines the purposes for which employees can use a private device. Also, ensure employee and guest BYOD devices such as mobile phones have separate Wi-Fis outside the corporate network.
Ensure Devices Go Offline Automatically in Case of a Threat
Even top-tier ransomware requires at least a few minutes between infecting a device and connecting with the hacker’s command and control (C&C) server. The security team can set up devices in a way that cuts them off from the network and Internet automatically if a suspicious process takes place.
Without access to the Internet, the ransomware remains idle on an infected device, and the security team can remove the threat without risking other systems.
What to Do If Your Computer Is Infected with Ransomware?
If your company falls victim to ransomware despite all the precautions, you need a disaster recovery plan. A typical response is to go through the following steps:
- Isolation: Isolate the infected system from the rest of the network. Shut down the device, pull out the network cable, and turn off the Wi-Fi to localize the problem.
- Malware identification: Next, determine what type of malware has infected the system. Either the IT team or an outside consultant should analyze and identify the threat.
- Report the breach: Even if some regulation does not oblige you to report an attack, authorities can offer expertise and insights the in-house team perhaps lacks.
- Remove the malware: Remove the malware by uninstalling everything on the infected device and reinstalling the operating system.
- Analyze data loss: Identify which data the attacker managed to encrypt. Also, search for signs of data exfiltration.
- Recover data: Once you contain the attack, restore data from the most recent backup available.
- IT forensics: Most hackers try to leave a back door in each system they infect. Ensure the team scans all IT environments for potential entry points.
- Improve the system: Determine how the intruder breached the system and make improvements to ensure the same attack does not happen again.

Read about cyber kill chains, a security strategy that allows companies to stay one step ahead of cybercriminals.
Should You Pay the Ransom?
In most cases, you should not pay the ransom to get your data back. Robust prevention measures and backups should prevent data loss if an attack takes place.
Even if you do not have a data backup, paying the ransom is still a risk. You have no guarantee that you will receive the decryption key, nor that the hacker will not sell the data after you send the payment. Additionally, your willingness to pay will also paint you as a target for future attacks.
Instead of paying the ransom, ensure you are never in a position where the only way to recover from an attack is to meet the criminal’s demands.
Know How to Prevent Ransomware and Stay a Step Ahead of Hackers
A proactive approach to stopping ransomware is the best way to keep your business safe. Implement the suggestions outlined above and create a disaster recovery plan to stay ahead of hackers and avoid needless monetary losses and reputation damage. Also, check out our ransomware detection guide to learn about the different techniques for detecting ransomware attacks or learn more about the differences between Malware vs Ransomware and how they work in our detailed guide.



