Introduction
Vault stores, controls, and protects the data used for authentication and authorization. Vault is a management system for secrets, restricting or approving access to passwords, certificates, or APIs. It also provides data encryption, on-demand secrets, and revocation.
In this tutorial, learn how to install Vault on CentOS and run Vault as a service.
Prerequisites
- A CentOS Linux system
- A user account with sudo privileges
- Access to a command-line/terminal window (Ctrl+Alt+F2)
Install Vault from Binary on CentOS
1. Before installing Vault, create a new directory in Linux using the mkir command to store the binary package and other necessary data for the software. To illustrate, we will name it “directory” and run the following command to create it:
sudo mkdir -p /opt/vault/directory2. With the directory set up, move on to downloading the binary from Vault’s official website. Navigate to the website and click on the blue Download icon.
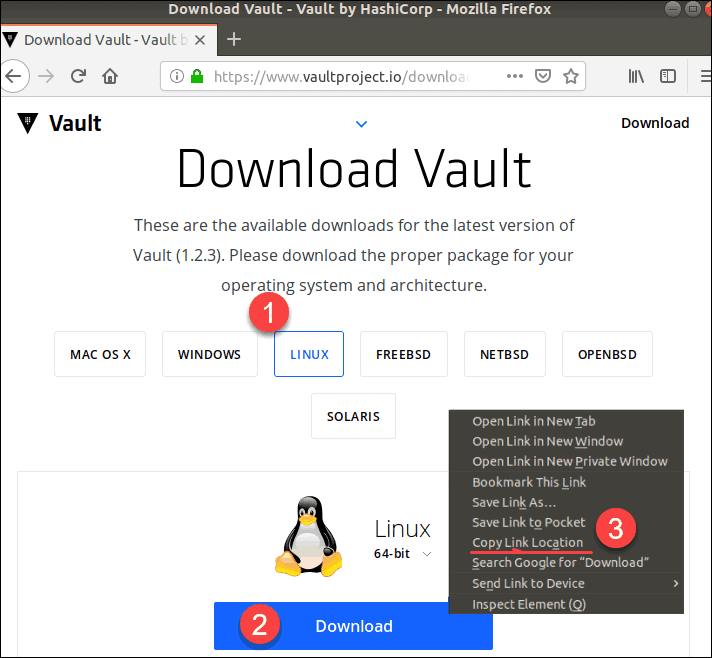
3. Find the appropriate package for your CentOS operating system (Linux) and click on the tile.
4. You will see the Linux icon and a Download button. Right-click on the button and select Copy Link Location.
5. Next, go back to the command line. Use the wget command and the link location you copied in the previous step to download the binary:
sudo wget https://releases.hashicorp.com/vault/1.2.3/vault_1.2.3_linux_amd64.zip6. Then, unzip the package using the command:
unzip vault_1.2.3_linux_amd64.zip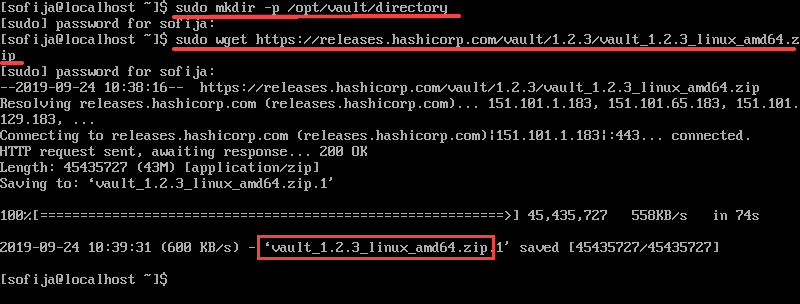
7. After unzipping, type:
sudo chown root:root vaultsudo mv vault /usr/local/bin/ (or to som other DIR that's present in your $PATH8. Verify Vault is running with the command:
vault --versionThe output displays the version of Vault running on the system.
For additional information, you can prompt the help page with the command:
vaultNote: Vault 1.2.3 is currently the newest version. However, newer releases may be available by the time of your installation.
Configuring Vault
Create a Service User for Vault
It is best to consider privileged account security and have a separate non-privileged system user for running a Vault server.
Use the following command to create a system user and grant ownership of the installation directory:
sudo useradd --system -home /etc/vault.d - shell /bin/false vaultCheck to see if you have successfully created the service user with:
sudo grep vault /etc/passwdThe output should show something like the line below:
vault:x:997:995::/etc/vault.d:/bin/falseRun Vault as a Service
To run Vault as a service, you also need to create a new Systemd service file:
sudo vi/etc/systemd/system/vault.serviceThen, add the content below:
[Unit]
Description="HashiCorp Vault - A tool for managing secrets"
Documentation=https://www.vaultproject.io/docs/
Requires=network-online.target
After=network-online.target
ConditionFileNotEmpty=/etc/vault.d/vault.hcl
StartLimitIntervalSec=60
StartLimitBurst=3
[Service]
User=vault
Group=vault
ProtectSystem=full
ProtectHome=read-only
PrivateTmp=yes
PrivateDevices=yes
SecureBits=keep-caps
AmbientCapabilities=CAP_IPC_LOCK
Capabilities=CAP_IPC_LOCK+ep
CapabilityBoundingSet=CAP_SYSLOG CAP_IPC_LOCK
NoNewPrivileges=yes
ExecStart=/usr/local/bin/vault server -config=/etc/vault.d/vault.hcl
ExecReload=/bin/kill --signal HUP $MAINPID
KillMode=process
KillSignal=SIGINT
Restart=on-failure
RestartSec=5
TimeoutStopSec=30
StartLimitInterval=60
StartLimitIntervalSec=60
StartLimitBurst=3
LimitNOFILE=65536
LimitMEMLOCK=infinity
[Install]
WantedBy=multi-user.targetEnable and start the service with the commands:
sudo systemctl enable vault.servicesudo systemctl start vault.servicePrepare to Administer Vault
The next step is to move the Vault bin directory to the PATH environment variable with the command:
export PATH=$PATH:/opt/vault/bin
echo "export PATH=$PATH:/opt/vault/bin" >> ~/.bashrc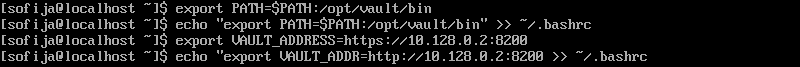
Followed by setting the environment variables for Vault by typing:
export VAULT_ADDRESS=http://10.128.0.2:8200
echo "export VAULT_ADDR=http://10.128.0.2:8200" >> ~/.bashrcInitialize and Unseal your Vault
To initialize and unseal Vault, you will first need to start Vault as a server in the dev mode. However, make sure not to run a dev server in production.
Run the following command:
vault server -devThe command produces an output that includes the server configuration, the unseal key, and root token. Save the unseal key and root token values, as you will need them in the next steps.
Note: As Vault does not fork, you need to open another shell or terminal to run the following commands.
Start by setting the environment variable. You will find this command as part of the output from the previous steps:
export VAULT_ADDR=’http://127.0.0.1:8200’Then, run the following command with the information from the dev server’s output:
export VAULT_DEV_ROOT_TOKEN_ID=”XXXXXXXXXXXXXXXX”Check the status of the server:
valut statusThe output should display that Vault is now initialized and no longer sealed.
Key Value
--- -----
Seal Type shamir
Initialized true
Sealed false
Total Shares 1
Threshold 1
Version 1.2.3
Cluster Name vault-cluster-18e6bce0
Cluster ID 16382125-eb14-f23a-8145-ad64eee072cf
HA Enabled falseConclusion
After reading this article, you have installed and configured Vault on CentOS 7 successfully. Although the installation includes numerous steps, if you follow the guide, you should not have any issues.