Introduction
Intel Security Guard Extensions (SGX) became available with the Skylake processor family. Intel SGX aims to provide an additional security layer that prevents malicious software execution even with admin privileges.
Employing the SGX model in your infrastructure, be it on-premises, public, private, or hybrid cloud, creates a trusted environment for processing sensitive data. PhoenixNAP Bare Metal Cloud offers a range of servers with SGX support.
This article will explain what Intel SGX is, how it works, and its benefits. We'll also show you how to choose a CPU that supports SGX when deploying a BMC server.
Requirements for Using Intel SGX
There are a few requirements for using SGX applications in your infrastructure:
- Your machine needs to have an Intel CPU that supports Intel SGX.
- The BIOS must have an option to enable SGX.
- The Intel SGX option must be set to Enabled or Software Controlled in BIOS, depending on the system. PhoenixNAP BMC servers have this option already enabled.
- You must Install the Intel SGX Platform Software package.
What is Intel SGX (Software Guard Extensions)?
Intel created Software Guard Extensions to improve data protection and enhance application code security. This CPU-based defense system allows applications to run in private memory space. Therefore, the exposure to inside and outside attacks at runtime is minimal.
Intel SGX allows developers to use CPU instructions to increase access control to:
- Prevent data modification and deletion.
- Prevent data disclosure.
- Enhance code security.
This instruction set of SGX-capable CPUs lets you encrypt portions of memory to guard valuable and sensitive data.
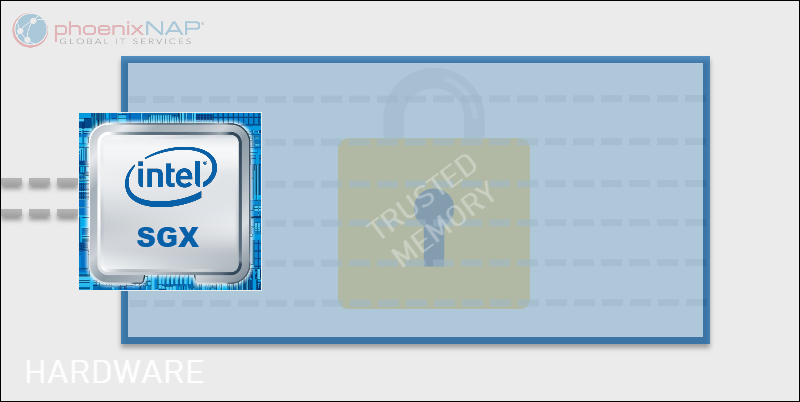
Such an environment provides a safe space for secrets when other parts of the infrastructure are compromised. This includes BIOS, firmware, root access, virtual machine manager, etc. When an application is protected with Intel SGX, its operation and integrity are unaffected in case of an attack.
The most sensitive data remains inaccessible to any process or user no matter the permission level. The reason is that an application runs inside a trusted memory segment that other processes cannot access.
What is SGX Enclave?
Enclaves are isolated areas of memory with sensitive application data protected by the CPU. The code and data in these memory regions are reachable only within the enclave. Using the Intel SGX SDK, developers create an instruction set to reserve a part of physical memory for this safe environment.
When you run an application inside an enclave, the CPU instantly encrypts it and stores the key. Since the key is inside the CPU, an attacker cannot obtain it by inspecting the system memory.
How Secure are Enclaves?
Enclaves are extremely safe environments for working with data. Access control is imposed inside these trusted memory parts, and not even physical access is sufficient to get hold of the protected data.
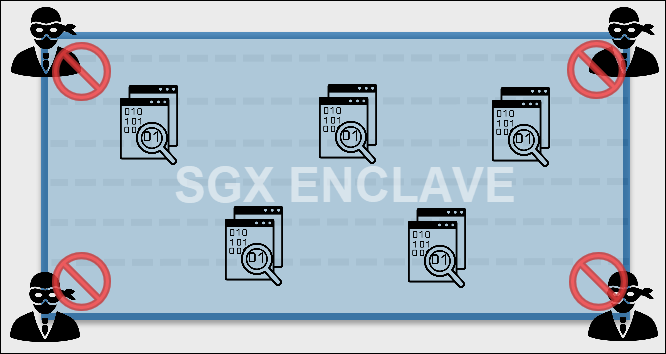
What makes enclaves secure is the automatic hardware encryption. The SGX technology uses the CPU to encrypt the information and store the key inside it. Hence, an external party cannot acquire the key and compromise the data. This means that not even the cloud provider can gain access.
Moreover, once the application exits or instructs the destruction of an enclave, all the information is lost with it.
How Does Intel SGX Work
When developing an Intel SGX application, the programmer can choose what to enclave. Every SGX application has two parts:
- Untrusted part
- Trusted part
The untrusted part is responsible for the enclave creation and system-wide communication. From here, an application calls only the specific trusted functions to access the data.
The trusted part stores the enclave created for processing sensitive data. The code and data are shown in clear text exclusively inside the enclave. The data that a trusted function returns stays in this secure memory area. The CPU rejects all external requests, and the enclave remains protected.
The application then resumes working in the untrusted part where it no longer has the insight into the sensitive data.
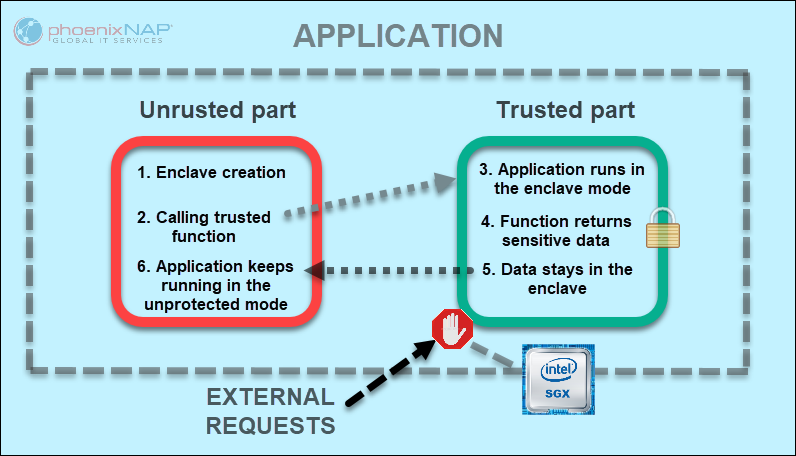
The application part that receives the secured data is in the untrusted section. An application can store the data outside the enclave once the CPU encrypts it. The encryption key stays in the enclave that contains the decrypting code and necessary algorithm. Therefore, the decryption is only possible on the same system where the data was sealed.
When to Use Intel SGX?
Intel SGX is an excellent tool for any context where confidential computing is a must. As this technology is native to the SGX-enabled CPUs, anyone who needs an additional security layer can use it.
Any industry can take advantage of the SGX capabilities, not only IT:
- Finance and Insurance
- Healthcare and social care
- Military
- Commerce
Since the data is protected while in use, Intel SGX is suitable for sharing information across multiple organizations. This model improves the control over which data to share, who can see it, for how long, and for what purpose.
Intel SGX Supported CPU
Starting with the Xeon scalable processors released from the 3rd quarter 2015 onward, all server processors support Intel SGX. Some of them are:
- Intel® Xeon® E-2288G
- Intel® Xeon® Gold 6326
- Intel® Xeon® Platinum 8352Y
Additionally, most desktop and mobile devices with 6th generation Intel Core CPUs support SGX.
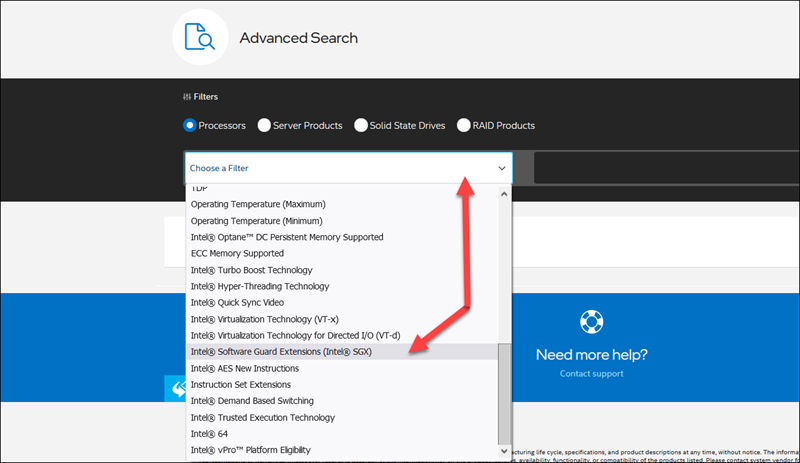
To check which Intel CPUs use SGX, refer to the Intel product search page. In the Choose a Filter drop-down menu, scroll down and select Intel® Software Guard Extensions (Intel® SGX).
Note: The system BIOS also needs to support Intel Software Guard Extensions.
How to Choose a CPU with SGX Support in the BMC Portal
To deploy a Bare Metal Cloud server with Intel SGX support:
1. Log in to the BMC portal.
2. Click the Deploy New Server button.
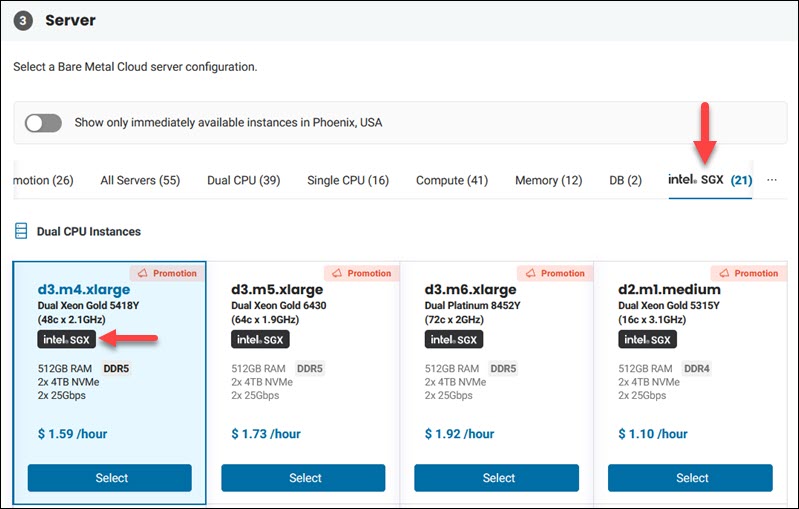
3. Locate the server with the Intel SGX logo in the Server section. Use the Intel SGX filter to narrow down the list.
4. Complete the process as with any other BMC server.
How to Enable Intel SGX in BIOS?
Note: Bare Metal Cloud servers. have Intel SGX enabled for you. No additional steps are necessary from your side to enable Intel SGX on our servers.
If a CPU and system BIOS support Intel SGX, then you can enable it. Use the corresponding key to enter the BIOS, depending on the manufacturer.
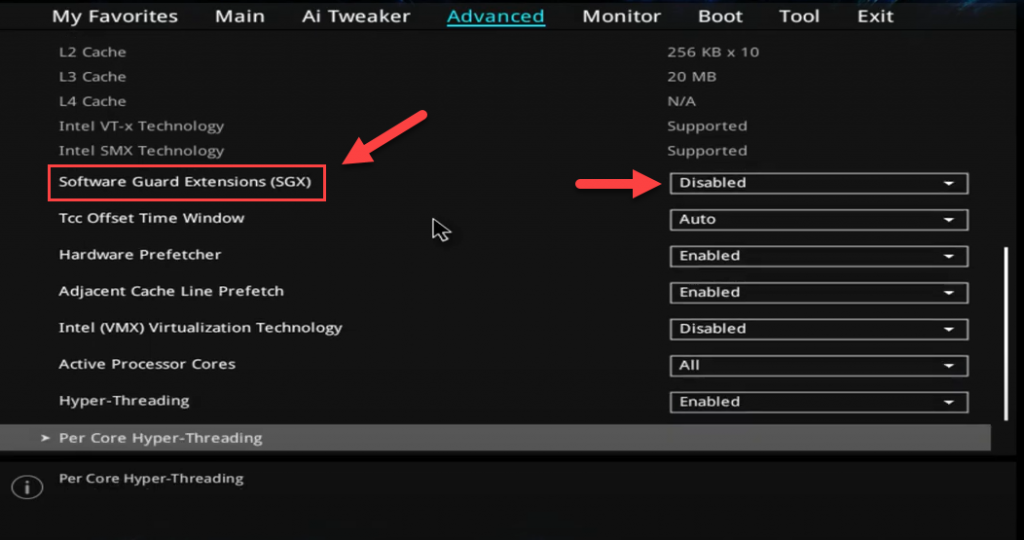
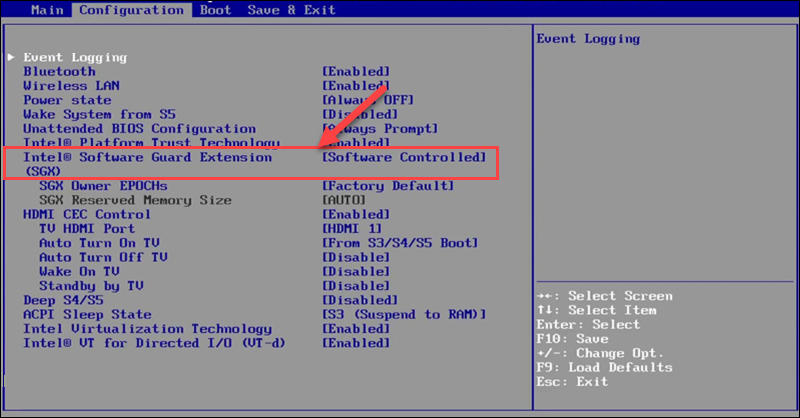
These are the possible SGX settings in BIOS:
- Disabled. The default setting for the Intel SGX option. In this mode, applications cannot enable SGX.
- Enabled. Applications can use Intel SGX. Makes sure the PRMRR configuration is correct for your system.
- Software Controlled. Allows an application to instruct BIOS to enable SGX automatically.
In some UEFI BIOS interfaces, the SGX is located under Advanced -> CPU configuration.
Some legacy BIOS interfaces have the Intel SGX option in the Configuration menu.
Should I Disable SGX?
The Intel SGX option is usually disabled by default. You can leave the settings at the default values. However, if you are using SGX applications, you must not disable this option in BIOS.
On the other hand, when the SGX option is enabled in BIOS, and you do not use SGX Applications or do not intend to, the feature may be disabled.
Intel SGX Benefits
There are many benefits to using Intel Software Guard Extensions. The obvious one is the increased security of sensitive and mission-critical data.
With Intel SGX, the information that needs to be verified can reside on the machine instead of sending it to a remote server. This includes biometric and other authentication data. Intel SGX protects from advanced threats that compromise BIOS, system components, and user profiles with root permissions.
Furthermore, data sealing provides the necessary protection of intellectual property even outside enclaves. The key for decoding the confidential data is in the trusted memory so that external access is blocked.
This model allows seamless horizontal scaling. As business demands rise, new machines can join the pool without disruption. Before becoming a part of the trusted server cluster, the nodes are verified to have the proper security level.
Note: To learn everything you need to know about Bare Metal Cloud, refer to our article What is Bare Metal Cloud.
Conclusion
The article explained the Intel SGX model, its main functionality, and showed how to tell if a CPU supports it.
To start using a server with full Intel SGX support, create a BMC account and choose your configuration.